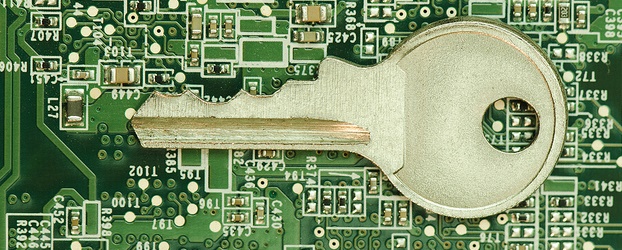
Encryption has become the most effective way for businesses of all sizes to best secure critical data. While it doesn’t prevent data from being accessible, it does render data unintelligible unless you have a secret key or password to decrypt or make the information readable.
With the introduction of Microsoft’s Windows BitLocker, business hardware (like servers, workstations, backup drives, etc.) can be protected by encryption; drastically improving the threat of data being stolen or exposed when a computer is lost or stolen. Encryption plays a significant role in data confidentiality on hardware and can be utilized in a variety of organizations including law firms, doctor office’s or businesses that supply laptops for employee’s use. Read more +