Smartphones and tablets have taken over personal computing landscape. Android dominates the sales market by sales volume, but Apple clearly has strong marketing, great products and dominates by profit margin. How does one move beyond the glimmer of a sleek looking product and make an educated decision between competing operating systems to determine which one will best meet their needs?
More important than choosing the right hardware, is selecting from multiple mobile operating systems (OS) the smartphone that will work best for your requirements. With more and more businesses allowing BYOD (Bring-Your-Own-Device) policies and using file sharing systems within the workplace, understanding key differences between operating systems will determine which devices you want accessing your company’s network.
Google’s Android vs. Apple iOS
While it is easy to get distracted by a great looking smartphone that feels lightweight, it is the differences in the OS ecosystem the device runs on that should remain your focus; particularly if you are looking to incorporate its use into business applications.
We’ve provided a brief overview on the main differences between the two OS’s here:
Applications
The common decision maker for most users are what applications (apps) are available to use within the OS. Sub-par app options are in large part to blame for the struggle Windows mobile phones have found in securing a strong foot hold in the marketplace.
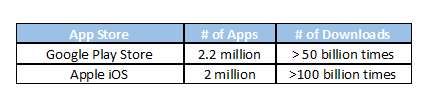
In 2015, Android had 1.4 billion active users on a monthly basis and yet its important to note that iOS still managed to make much more money that the Google Play store. The best selling OS since 2013, Android remains a popular choice among those looking for a low-cost system for high-tech devices.
Features
There are several common features that are shared among the mobile operating systems. However, Apple’s iOS superior continuity between its devices, is what will distinguish its features from an Android’s OS. Apple devices easily communicate and connect with each other. Many loyal users have bought into their ecosystem of products.
Within both OS’s you will find the following out-of-the-box:
- Free Messaging Apps:
- Google Hangouts, which only encrypts data while in transit, resulting in privacy limitations for users of Hangouts.
- Apple’s iMessage, which uses end-to-end encryption, making communication more secure.
- Health Tracking & monitoring Apps:
- Google Fit covers the basics of activity, weight and heart rate and logs common activities like walking, running and cycling.
- Apple Health is comprehensive web interface that covers the basics in addition to sleep tracking, distance, elevation, calories burned, etc.
- Personal Assistants:
- Google Now is available with Android 6.0 Marshmallow. It will provide contextual information based on what is on the screen at the time.
- Apple’s Siri understands what you are saying and feels more like an actual assistant.
Security
Security should be on the forefront of every user’s mind since 2016 has been full of security attacks on businesses. These two mobile operating systems tackle security in the following ways:
- Fingerprint Technology:
- Android fingerprint technology varies by manufacturer, which has led to a number of security breaches. Some manufactures store fingerprints unprotected which means criminals could (and have) easily read and extracted user’s fingerprints. It is only since Android 6.0 that there has been a native fingerprint API included with devices.
- With iOS, the technology is more than just a convenient way to unlock your device but uses comprehensive bio-metrics and stricter implementation guidelines.
- Backups:
- Google’s backup solution isn’t quite as comprehensive as Apple’s. Their solution is more about individual pieces being saved, that can then be accessed at any time from any device that you’ve signed into Google with.
- With iCloud/iTunes all of your apps, contacts, photos, and home screen layout will be backed up. They can be scheduled to happen automatically (even over Wi-Fi), and if you encrypt the backup you can even restore passwords and credentials to the apps you use.
Unfortunately developer confusion and limited documentation has resulted in Android apps routinely requesting unnecessary permissions to other apps and device features. Not only does this reduce their effectiveness but it has opened Android devices up to number of malware vulnerabilities.
Updates
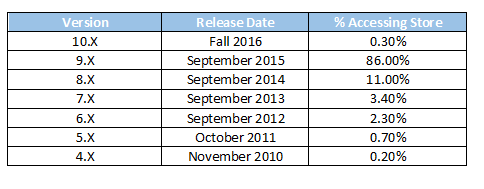
Major version updates of iOS are released annually and push notifications are sent to every device. This means users of Apple devices are given the opportunity to run the latest security patches and upgrades.
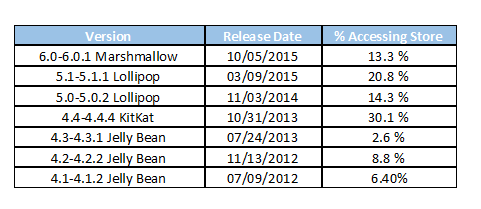
Android has no centralized update system for its devices. This means that not only do most devices fail to receive regular security updates, but there is a lack of continuity among the OS versions the devices are using (as shown in chart below). As a result, users may find certain apps and features are not compatible with the version OS they are running. Google licenses their mobile software and Android trademarks only to manufacturers that meet their compatibility standards. It is then up to the hardware manufacturer to push available updates to the Android device. As a result, Android devices seem to age faster, and upgrading to a new phone may be the only option left to consider.
In June 2016 the following breakdown showed the Android versions that were accessing the Google Play store:
Compared to the iOS versions that are accessing the App store:
In 2015, it was concluded that 90% of Android phone in use had known but unpatched security vulnerabilities due to lack of updates. The success of Android has made it a target for malware, viruses and other security threats.
Things to Consider
The iOS is all about providing users with an experience that is simplistic, secured and connected—to Apple’s ecosystem. Google allows for a more customizable interface, and allows users access to its services, content and apps on both Android and iOS devices. While each mobile operating system has certain limitations and quirks, iOS has superior support, updates and apps which is what you’ll find your team needs to be organized, productive and accessible while in and outside your organization’s network.
Whichever mobile devices you allow your employees to integrate be sure to have a strong BYOD policy in place. Clearly specifying what apps and devices are allowed/banned and aligning these policies with a clear employee exit strategy should go far in protecting your network infrastructure.
(image via Flickr/Maurizio Pesce)